CVE-2025-0033
AMD SEV-SNP Memory Integrity Vulnerability
Description
Improper access control within AMD SEV-SNP could allow an admin privileged attacker to write to the RMP during SNP initialization, potentially resulting in a loss of SEV-SNP guest memory integrity.
INFO
Published Date :
Oct. 14, 2025, 3:16 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2025-0033
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | MEDIUM | b58fc414-a1e4-4f92-9d70-1add41838648 | ||||
| CVSS 3.1 | MEDIUM | [email protected] |
Solution
- Update AMD SEV-SNP firmware.
- Verify RMP access controls during initialization.
- Apply relevant security patches.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-0033.
| URL | Resource |
|---|---|
| https://www.amd.com/en/resources/product-security/bulletin/AMD-SB-3020.html |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-0033 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-0033
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-0033 vulnerability anywhere in the article.
-
Daily CyberSecurity
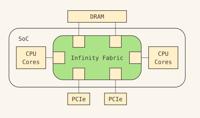
Fabricked: The 100% Deterministic Attack Breaking AMD’s Confidential Computing Vault
Schematic overview of the Infinity Fabric In the high-stakes world of cloud security, the promise of Confidential Computing is simple: your data should be safe even from the person owning the server. ... Read more

-
Hackread - Latest Cybersecurity, Hacking News, Tech, AI & Crypto
Microsoft Patch Tuesday Oct 2025 Fixs 175 Vulnerabilities including 3 Zero-Days
Microsoft Patch Tuesday for October 2025 was massive, delivering over 170 security fixes, making immediate patching mandatory due to the volume and critical nature of the vulnerabilities across Window ... Read more

-
The Register
Frightful Patch Tuesday gives admins a scare with 175+ Microsoft CVEs, 3 under attack
Spooky season is in full swing, and this extends to Microsoft's October Patch Tuesday with security updates for a frightful 175 Microsoft vulnerabilities, plus an additional 21 non-Microsoft CVEs. And ... Read more
The following table lists the changes that have been made to the
CVE-2025-0033 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Oct. 14, 2025
Action Type Old Value New Value Added Description Improper access control within AMD SEV-SNP could allow an admin privileged attacker to write to the RMP during SNP initialization, potentially resulting in a loss of SEV-SNP guest memory integrity. Added CVSS V3.1 AV:L/AC:L/PR:H/UI:N/S:C/C:N/I:H/A:N Added CWE CWE-284 Added Reference https://www.amd.com/en/resources/product-security/bulletin/AMD-SB-3020.html